InAppBrowser reveals if TikTok, Instagram and other apps with browsers inject their JavaScript
Eleanore Beatty August 20, 2022 ArticlePreviously this thirty day period it was exposed that well-liked cell programs with integrated browsers injected custom made JavaScript into frequented web pages. Facebook, Instagram and TikTok all use code injection methods to practically monitor just about anything that application buyers do on any web-site that is opened in the in-application browser.
The corporations that own the offending apps benefit from this in various techniques. Initially, because every little thing transpires solely powering the scenes, with no most end users suspecting any of that. Next, for the reason that the in-app browsers do not assist content blockers or expose privacy data when used.
Most organizations use in-app browsers and code injections for tracking and monetization uses, but some might use code to check all person activity, together with all keystrokes.
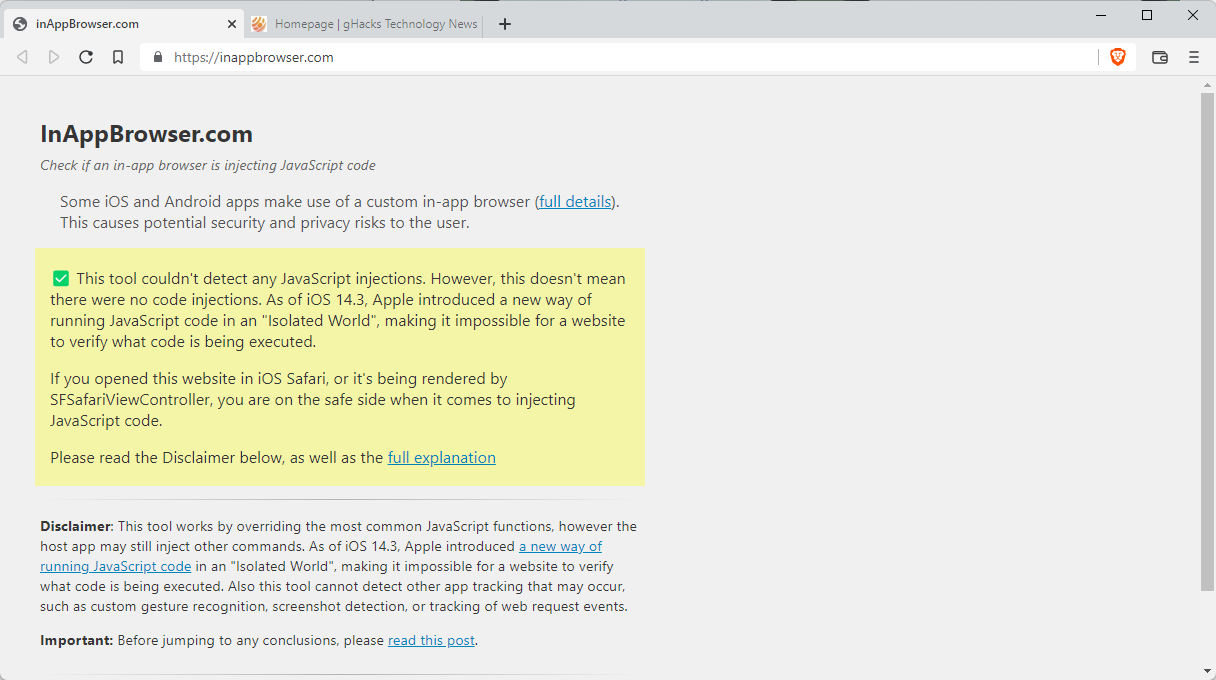
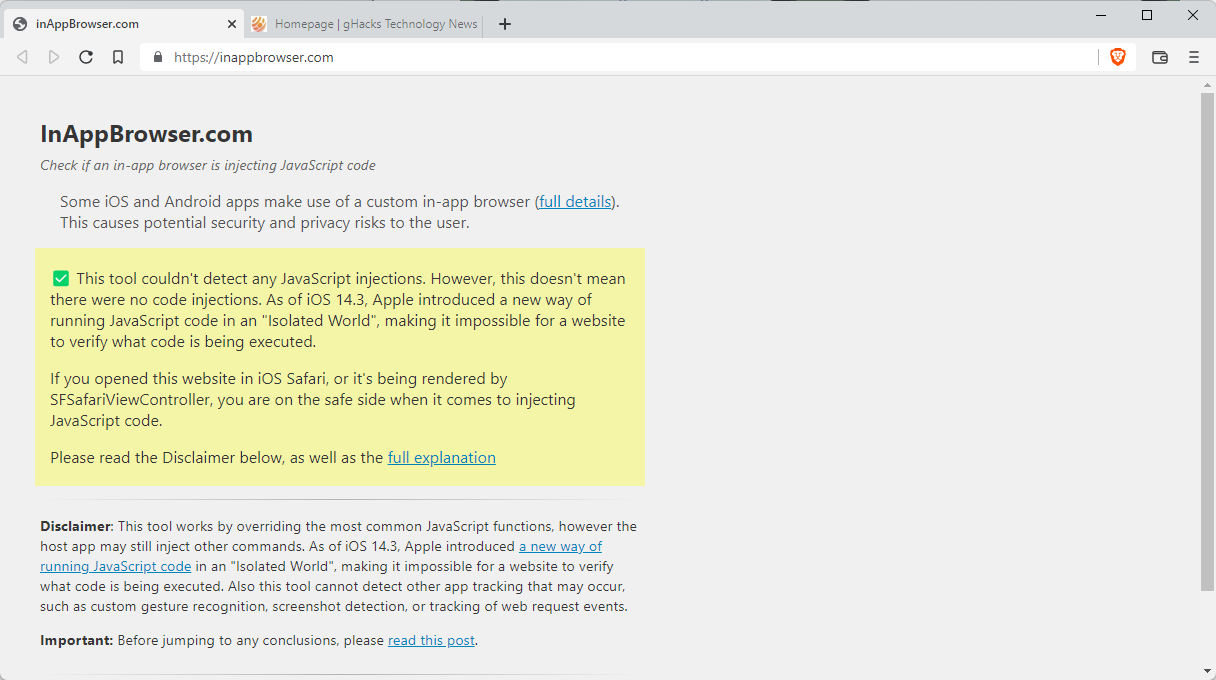
Felix Krause designed the site InAppBrowser, which is developed to reveal to the consumer if an in-application browser is injecting code.
Below is how it will work:
- Open up the application that you want to analyze.
- Use share performance within the application to get the website link https://InAppBrowser.com into the application. You may well DM a call or article publicly.
- Open the backlink that has just been shared or posted.
- Verify the report that is shown.
The site reveals if it detected JavaScript code injections and how it charges these injections. For TikTok, the web-site reveals the adhering to:
- Adds CSS code, lets application to customise overall look of internet site.
- Monitors all taps going on on internet sites, which includes taps on all buttons & backlinks.
- Screens all keyboard inputs on internet sites.
- Gets the web page title.
- Receives information and facts about an ingredient primarily based on coordinates, which can be made use of to track which components the person clicks on.
Instagram, a different preferred application, injects JavaScript code as perfectly. Whilst it does not keep track of keyboard inputs, it does monitor all JavaScript messages and all text picks, and injects exterior JavaScript code.
All detected JavaScript instructions are outlined as effectively for deeper inspection.
You can check out out the blog site put up, which offers additional particulars.
Krause notes that the website may perhaps not detect all code injections or all executed JavaScript commands. Also, it does not detect indigenous code, which applications may well use as perfectly.
Protection from invasive in-browser apps
Mobile application people have just a several options. Apart from the evident, taking away the app from the unit, they could be in a position to redirect backlinks to other browsers on the gadget. Not all applications assist that though. The use of DNS-based written content blockers may possibly not enable as substantially possibly, at the very least not from the potential reading of keystrokes or other routines unrelated to the show of ads or monitoring.
Now You: Do you use applications with in-app browsers?
Summary
Post Name
InAppBrowser reveals if TikTok, Instagram and other applications with browsers inject their JavaScript
Description
Some applications use in-application browsers to screen internet articles InAppBrowser reveals if code is injected for monitoring, monetary or other gains.
Writer
Martin Brinkmann
Publisher
Ghacks Technology News
Symbol

Advertisement
You may also like
Archives
- December 2024
- November 2024
- September 2024
- August 2024
- July 2024
- February 2024
- January 2024
- December 2023
- November 2023
- October 2023
- September 2023
- August 2023
- July 2023
- June 2023
- May 2023
- April 2023
- March 2023
- February 2023
- January 2023
- December 2022
- November 2022
- October 2022
- September 2022
- August 2022
- July 2022
- June 2022
- May 2022
- April 2022
- March 2022
- February 2022
- January 2022
- December 2021
- November 2021
- October 2021
Calendar
| M | T | W | T | F | S | S |
|---|---|---|---|---|---|---|
| 1 | 2 | 3 | 4 | 5 | 6 | |
| 7 | 8 | 9 | 10 | 11 | 12 | 13 |
| 14 | 15 | 16 | 17 | 18 | 19 | 20 |
| 21 | 22 | 23 | 24 | 25 | 26 | 27 |
| 28 | 29 | 30 | 31 | |||
